Tech. Intelligence Curation By Brian French | April 24, 2026
Created with the assistance of Claude 3.5 verified actual cases and premise via Gemini 1.5.
Mastering Cybersecurity Communications to Protect Corporate Integrity, Stakeholder Trust, and Market Value After a Critical Technical Failure
A Strategic Deep Dive for the Florida Senior Business Officer — 2026
Executive Summary: The First Hour Will Define the Next Decade
Why Data Breach Communications Is No Longer an IT Problem
A modern data breach is not a technical event that requires a communications response. It is a communications event that happens to have a technical origin. That distinction — which most organizations still get wrong — is the difference between a painful recovery and a company-ending crisis.
For Florida senior business officers, the pressure has never been higher:
- The global average cost of a data breach reached $4.88 million in 2024, a 10 percent year-over-year increase
- Financial-sector breaches now average $6.08 million per incident
- Human error directly caused 60 percent of all breaches in the 2025 Verizon Data Breach Investigations Report (DBIR)
- Business Email Compromise (BEC) losses hit $6.3 billion globally in 2025 — median loss: $50,000 per incident
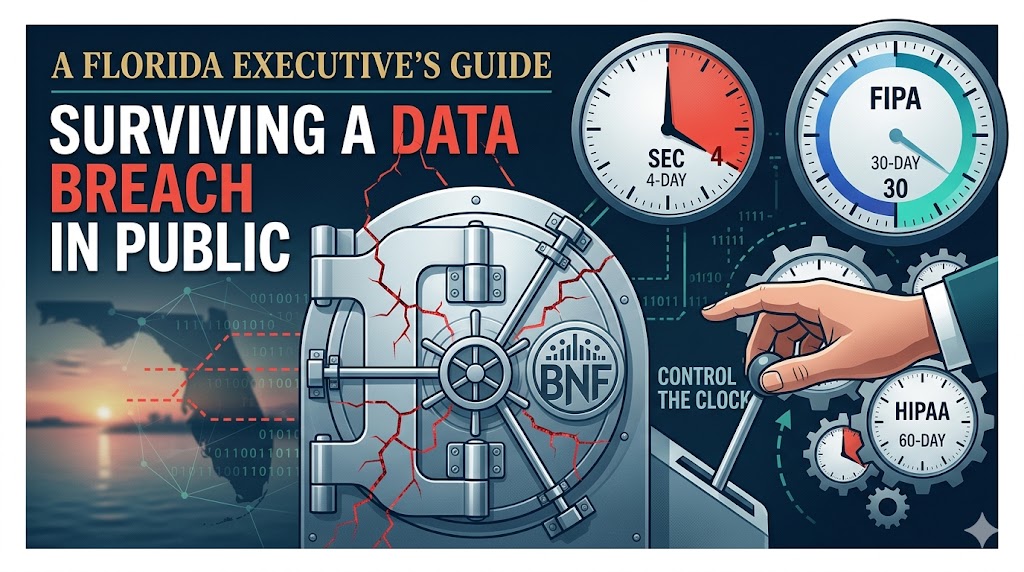
- The SEC now requires public companies to disclose material cybersecurity incidents within four business days on Form 8-K Item 1.05
- Florida’s FIPA statute requires notification within 30 days — one of the most aggressive state timelines in the country
The defining new reality: SEC, HIPAA, FIPA, state attorneys general, class-action plaintiffs’ attorneys, and journalists are all watching the same clock. Every hour a company delays, three different legal clocks get shorter and the narrative gets harder to control.
This article maps the regulatory landscape, documents five verified breach case studies, delivers a first-48-hours playbook, and closes with a curated directory of Florida-based resources for the senior officer who will be answering the board’s questions on Monday morning.
Part I — The Modern Breach Regulatory Environment
Three Clocks Are Running at Once
Once a Florida senior officer knows a breach has occurred, three independent regulatory deadlines start ticking simultaneously — and they do not wait for each other.
Clock One — The SEC’s 4-Day Window (Public Companies)
Under SEC Form 8-K Item 1.05, effective since December 18, 2023, any SEC-registered public company must disclose a material cybersecurity incident within four business days of determining materiality.
- Smaller reporting companies became subject to the rule on June 15, 2024
- Disclosure must describe the nature, scope, and timing of the incident and its material impact or reasonably likely material impact
- Ransomware payment and insurance reimbursement do not remove the materiality — if the event was material, it must be disclosed
- The SEC now routinely sends comment letters to companies whose 8-Ks appear to understate impact
In October 2024, the SEC took a critical enforcement step: settled enforcement actions against four companies for cybersecurity disclosure failures, including one company found to have “negligently made materially misleading misstatements” in its Form 8-K regarding a cyberattack.
The precedent is set: Minimizing a breach in your 8-K is now its own enforcement risk — independent of the breach itself.
Clock Two — Florida’s 30-Day FIPA Window (All Businesses)
The Florida Information Protection Act (FIPA), codified at Florida Statutes § 501.171, applies to any business — of any size, incorporated anywhere — that handles personal information belonging to a Florida resident.
Key FIPA requirements every senior officer must know:
- Notify affected Florida residents within 30 days of determining a breach has occurred
- Notify the Florida Department of Legal Affairs if 500 or more Florida residents are affected
- No small-business exemption — FIPA applies regardless of revenue or employee count
- Notification may only be delayed if it would interfere with an active criminal investigation
- Substitute notice (media/website only) is available only if costs exceed $250,000 or more than 500,000 individuals are affected
- Third-party agents must notify the covered entity within 10 days — but the covered entity still owns the consumer notification obligation
Clock Three — HIPAA, GLBA, and Sector-Specific Rules
For Florida healthcare, financial services, and insurance entities:
- HIPAA Breach Notification Rule requires notification within 60 days of discovery for protected health information
- GLBA and Florida Office of Insurance Regulation rules may trigger additional notifications
- OCR (HHS Office for Civil Rights) may open its own investigation — as it did aggressively in the Change Healthcare episode
The Florida Regulatory Surface Is Larger Than Most Officers Realize
Florida’s regulatory environment is uniquely dense for a non-California state. The Florida Digital Bill of Rights (FDBR), effective July 1, 2024, adds another layer for large data controllers that meet specific revenue and processing thresholds. A single breach can trigger FIPA, FDBR, HIPAA, and SEC obligations simultaneously — and each has a different clock, different content requirement, and different penalty regime.
Part II — Five Breach Case Studies Every Florida Executive Should Know
Each case below is drawn from documented public record. Each illustrates a distinct failure mode or success pattern.
Case 1 — Equifax (2017)
The Textbook of What Not to Do, Still Studied Nearly a Decade Later
In 2017, Equifax suffered one of the most consequential data breaches in U.S. history:
- 147.9 million American consumers had their personal data exposed
- Exposed data included Social Security numbers, birth dates, addresses, driver’s license details, and credit card information
- The root cause was an unpatched vulnerability in Apache Struts (CVE-2017-5638) — for which a patch had been available since March 2017
- Attackers (later attributed by the U.S. Justice Department to four members of China’s People’s Liberation Army) maintained access from May through July 2017
- Equifax waited six weeks after discovering the breach to alert consumers
The communications response compounded the technical failure:
- Consumers were directed to an incorrectly configured website (equifaxsecurity2017.com) that Equifax’s own official Twitter account later mistakenly linked to a phishing clone
- Consumers were asked to provide additional personal information (including partial Social Security numbers) to check whether their data had been exposed — in the middle of a data breach
- Three Equifax executives sold company stock before the breach was public
- Total cost to Equifax exceeded $1.38 billion in settlements, fines, and remediation
Brian’s Takeaway: The technical breach is the first crisis. Your response to it is the second crisis — and the second crisis is typically worse. Every single post-breach action must be stress-tested by someone who is not from your IT or legal team, because those teams are optimizing for different objectives than your customers.
Case 2 — MGM Resorts (September 2023)
$100 Million Lost in Ten Days Because of a Ten-Minute Phone Call
In September 2023, the threat actor group Scattered Spider — working under the umbrella of the Russia-linked ALPHV/BlackCat ransomware operation — compromised MGM Resorts through a social-engineering phone call to the IT help desk.
How it happened:
- Attackers identified an MGM employee on LinkedIn
- Called the help desk impersonating that employee
- Convinced help desk staff to reset the user’s multi-factor authentication
- Pivoted through MGM’s Okta identity provider into its VMware infrastructure
- Encrypted more than 100 ESXi hypervisors
The operational and financial damage:
- 10-day shutdown across more than 30 properties, including Bellagio, Mandalay Bay, and the Cosmopolitan
- Malfunctioning slot machines, disabled ATMs, inoperative digital key cards, broken payment systems — in some cases, MGM reverted to pen-and-paper operations
- MGM disclosed to the SEC a $100 million hit to Q3 2023 Adjusted Property EBITDAR, with an additional ~$10 million in one-time consulting, legal, and advisory costs
- Revenue losses ran approximately $8.4 million per day during the outage
- MGM’s stock dropped approximately 4 percent in the days following disclosure
- In 2025, MGM reached a $45 million class-action settlement covering both the 2019 and 2023 breaches
The communications response was a mixed result. MGM issued a same-day public statement on X on September 11, 2023, and followed with additional updates. CEO Bill Hornbuckle later characterized the attack as “corporate terrorism at its finest” at the Global Gaming Expo — a framing that emphasized the company as a victim rather than a party with preventable controls gaps. MGM chose not to pay the ransom, aligning with federal law enforcement guidance, while rival Caesars Entertainment (hit by the same threat actor group) reportedly paid.
Brian’s Takeaway: A $33.9 billion enterprise was compromised by a 10-minute phone call. The most important cybersecurity control in your company today may not be technical — it may be a help-desk identity-verification protocol. And when your CEO speaks publicly, “corporate terrorism” language may feel correct but shifts the narrative away from what the company will do differently — which is what customers, regulators, and the SEC actually want to hear.
Case 3 — Change Healthcare / UnitedHealth Group (February 2024)
The $2.4 Billion Cautionary Tale of Opaque Disclosure
On February 21, 2024, UnitedHealth Group disclosed that its Change Healthcare subsidiary — the largest medical claims clearinghouse in the United States — was under a cyberattack. The BlackCat/ALPHV ransomware group claimed responsibility.
The scale was extraordinary:
- CEO Andrew Witty testified at a House hearing in May 2024 that the breach may have exposed the data of approximately one-third of all Americans
- UnitedHealth paid a reported $22 million ransom
- Total estimated cost ballooned to $2.457 billion by Q3 2024
- Pharmacies, hospitals, and medical practices were unable to process claims for weeks, with particular pain for smaller and rural providers
The communications response drew bipartisan Congressional condemnation:
- UnitedHealth initially stated it was “not announcing an official breach notification at this time” — creating confusion about which covered entities bore HIPAA notification obligations
- HHS OCR took the unusual step of issuing a “Dear Colleagues” letter reminding covered entities of their regulatory obligations
- Senators Blumenthal (D-CT) and Hawley (R-MO) sent a scathing letter demanding information
- Senators Blackburn (R-TN) and Hassan (D-NH) said the company “should have done this months ago” when notifications finally began in mid-2024
- Rep. Cathy McMorris Rodgers (R-WA), then-chair of the House Energy and Commerce Committee, stated UnitedHealth’s handling would likely be “a case study in crisis mismanagement for decades to come”
Brian’s Takeaway: When the affected population is one-third of Americans, there is no communications strategy that ends well — but “we are not announcing an official breach notification at this time” is the single most dangerous sentence a company can publish in that environment. It invites exactly the Congressional, regulatory, and class-action response UnitedHealth received. Name the event. Own the timeline. Update publicly.
Case 4 — Maersk and NotPetya (June 2017)
The Gold Standard of Transparent Breach Response
On June 27, 2017, the NotPetya malware — launched by Russian military intelligence as an attack on Ukraine — became the most damaging cyberattack in history. Among its victims was A.P. Møller-Maersk, the world’s largest container shipping company, which handles roughly one-fifth of global container traffic.
The technical impact was catastrophic:
- Maersk’s network was crippled within seven minutes
- Most of the damage was done within an hour
- Maersk had to reinstall 4,000 servers, 45,000 PCs, and 2,500 applications over ten days
- The Active Directory system took nine days to restore
- Total estimated cost: $250–$300 million
But the communications response became a case study in what to do right:
- CEO Søren Skou was personally involved in all crisis calls from the outset
- Maersk sent daily public updates via the website and Twitter on which ports were open and closed, which booking systems were running, and what was being done
- When IP phones were inoperable, the team pivoted to WhatsApp groups and personal email to maintain customer contact
- Communications were fact-based, not speculative
- Maersk apologized upfront and then redirected focus to resolution
- Frontline staff were instructed to do whatever was necessary for customer satisfaction, regardless of cost
The result was counterintuitive. Maersk’s share price went up in the aftermath of the attack. Customers’ first response was reportedly, “How can we help?” CISO Andy Powell later summarized the philosophy: “Transparency is everything. Our clients at Maersk loved the fact that we told them on day one what was going on, and we included them throughout in what we were doing.”
Brian’s Takeaway: A $300 million catastrophic loss resulted in a stock-price increase because the company treated the breach as a shared problem with its customers rather than an embarrassment to be managed. Transparency is not a risk — opacity is the risk. Daily fact-based updates, led from the CEO’s office, with a clear apology upfront, are the textbook sequence.
Case 5 — Snowflake Customer Breach Cascade (2024)
When the Weakest Link Is Your Customer’s Identity Hygiene
In 2024, Mandiant (Google Cloud’s incident-response unit) tracked the threat actor UNC5537 — a financially motivated group that stole significant volumes of records from Snowflake customer accounts and extorted the breached organizations.
What made this case different:
- The compromise was not a breach of Snowflake’s infrastructure
- Attackers used credentials harvested from earlier, unrelated infostealer malware infections on employee and contractor endpoints
- Customers affected included AT&T, Ticketmaster, Advance Auto Parts, and approximately 165 other Snowflake customers
- The common denominator: customers had not enforced multi-factor authentication on Snowflake accounts
- AT&T paid a reported $370,000 ransom and had data on approximately 109 million customer accounts exposed
The communications lesson is structural. Organizations have learned to communicate about their own breaches. Almost none have rehearsed how to communicate about a third-party SaaS breach in which their customers’ data was exposed — but the accountability is, legally and reputationally, still largely theirs.
Brian’s Takeaway: Your cloud providers’ breaches are increasingly your breaches. Third-party risk management (TPRM), MFA enforcement on all SaaS tenants, and pre-drafted third-party-breach holding statements are now core infrastructure. When your SaaS vendor is compromised, the journalist calling at 6 p.m. wants to know what you are doing for your customers — not what your vendor is doing for you.
Part III — The Senior Officer’s First 48 Hours Playbook
A Minute-by-Minute Protocol You Can Hand to the Board
This protocol synthesizes the case-study lessons into a working sequence. It assumes that your incident response infrastructure is already in place. If it is not, every hour compresses.
HOURS 0–4 — Containment and Assessment
- Activate the pre-designated incident response team. Roles must already be assigned: Incident Commander, Legal Counsel, External Counsel, CISO, Head of Communications, Head of Investor Relations, Chief Customer Officer. If you are assigning roles during the incident, you are already late.
- Engage outside breach counsel under privilege. Attorney-client privilege is one of the few protections available during forensic investigation. Early engagement is a board-level control.
- Preserve forensic evidence. Do not rebuild until the forensic team has captured what is necessary. Rebuilding too early destroys evidence that plaintiffs’ attorneys, regulators, and law enforcement will later want.
- Brief the CEO and Board Chair. No external communication, internal or to customers, before this briefing is complete.
- Do not pay a ransom without structured deliberation. The decision has SEC, Treasury/OFAC, FBI, cyber-insurance, and reputational implications. The MGM-vs.-Caesars divergence in 2023 is instructive — both paths are defensible, but only with documentation.
HOURS 4–24 — Controlled Disclosure
- Issue an internal holding statement to all employees within 4 hours of confirmed breach. Employees will talk. Frame the narrative inside the company before it leaks outside.
- Issue an external holding statement within 24 hours if material. The statement must: acknowledge awareness, describe containment status in general terms, commit to an update window, provide a single authoritative channel for updates, and refuse to speculate on scope or attribution until forensic evidence supports the statement.
- Determine SEC materiality on a documented basis. If you are a public company, the four-business-day 8-K clock starts at the materiality determination — not at discovery. Document the determination process; the SEC will scrutinize it.
- File Item 1.05 (if material) or Item 8.01 (if not) on Form 8-K. The SEC’s post-2024 guidance strongly prefers that non-material incidents be disclosed under 8.01 to preserve the meaning of 1.05.
- Notify Florida Department of Legal Affairs if 500+ Florida residents are affected — within the 30-day FIPA clock.
HOURS 24–48 — Stakeholder Choreography
- CEO-led communication, not CCO-led. The Maersk precedent is clear: CEO visibility from day one builds trust. The Equifax precedent is clear: CEO invisibility destroys it. Your CEO must be prepared to speak, and to speak in plain English.
- Activate coordinated stakeholder notification:
- Customers — dedicated support line, identity protection services (standard: two years of credit monitoring), FAQ page that does not ask customers for additional sensitive information
- Employees — internal channel, HR support, clear guidance on what they can and cannot say
- Partners, vendors, and contractual counterparties — many contracts now have 24–72 hour notice requirements
- Regulators — SEC, HHS/OCR if applicable, Florida DLA, state attorneys general
- Law enforcement — FBI Field Office or CISA
- Cyber insurance carrier — delay in notice can void coverage
- Investors / analysts — if public, pre-brief is not permitted; treat all disclosures as simultaneous via 8-K
- Stand up a dark-site or incident microsite. Avoid the Equifax trap. The URL must be on your own primary domain (e.g.,
yourcompany.com/security-update), not a newly registered domain that looks like a phishing site. - Do not require customers to submit sensitive information to check exposure. Ever.
DAYS 3–14 — Sustained Communication and Rebuild
- Daily public updates in the first week. The Maersk playbook. Even if the update is “no material change,” the cadence itself is the trust-building mechanism.
- Avoid premature attribution. Attribution is a forensic and intelligence-community function — not a corporate communications function. Incorrect attribution invites litigation and diplomatic risk.
- Be precise about what you know, what you don’t, and when you’ll know more. Hedging language (“it appears that,” “at this time”) is acceptable when true. Hedging is unacceptable when used to obscure.
- Lead with customer remediation, not corporate defense. The J&J Tylenol principle applies to breaches: customers care about their exposure, not your reputation. Addressing the first produces the second.
DAYS 14–90 — Structural Change
- Deliver a board-level post-mortem with specific structural commitments. Johnson & Johnson’s Tylenol response set the standard: re-engineered packaging, industry-standard change, new federal regulation. The equivalent for a breach is: MFA enforced everywhere, identity-verification protocol at the help desk, third-party SaaS inventory, tabletop exercise cadence, and — critically — documented governance changes at the board level.
- Update your 10-K cybersecurity disclosures. Under SEC Reg S-K Item 106, your annual report must describe your processes for identifying and managing cybersecurity risk and the role of the board in oversight.
- Expect and prepare for litigation. Class-action plaintiffs’ firms are monitoring every 8-K and every FIPA notification. MGM reached a $45 million class settlement. Equifax exceeded $1.38 billion. The plaintiffs’ bar is well-capitalized and patient.
Part IV — Reputation as a Governed Asset
The Closing Principle for the 2026 Florida Executive
A breach will happen. Verizon’s 2025 DBIR, IBM’s Cost of a Data Breach, and every cyber insurer’s actuarial tables agree on this point — the only variable the senior officer controls is how the organization responds.
The Lesson of the Five Cases, in One Paragraph
- Equifax lost a decade of trust by delaying disclosure, misdirecting consumers, and requiring them to hand over more sensitive data in the middle of a breach.
- MGM survived operationally but paid $100 million plus $45 million in class settlements because a single help-desk call defeated a $33.9 billion company’s controls.
- UnitedHealth/Change Healthcare converted a $2.4 billion technical failure into a Congressional case study in mismanagement by publishing the phrase “not an official breach notification at this time.”
- Maersk absorbed a $300 million catastrophic loss and gained stock value because the CEO stood in front of it on day one and told the truth daily.
- Snowflake’s customer cascade reminded every senior officer that your vendors’ breaches are your breaches — and you must have pre-staged communications for that exact scenario.
In every case, the decisive factor was not the attack itself. It was the governance system, communications infrastructure, and leadership posture the organization had built before the attack — and the clarity of thought in the first 48 hours after it.
Part V — Florida Academic and Professional Resources
A Curated Directory for the Senior Officer
The following is a curated list of Florida-based institutions, regulatory bodies, and professional organizations relevant to cybersecurity, breach response, privacy law, and incident communications.
Academic Programs and Research Centers
University of Florida — Florida Institute for Cybersecurity Research (FICS). One of the nation’s leading academic cybersecurity research centers, housed within the Herbert Wertheim College of Engineering. Gainesville, FL. fics.institute.ufl.edu
University of South Florida — Bellini College of Artificial Intelligence, Cybersecurity and Computing. Home to an NSA-designated Center of Academic Excellence in Cyber Defense and robust graduate programs in cybersecurity, analytics, and information assurance. Tampa, FL. usf.edu/bellini-college
Florida International University — College of Engineering and Computing (Cybersecurity Programs). NSA/DHS-designated Center of Academic Excellence in Cyber Defense Education and Research. Offers B.S., M.S., and Ph.D. tracks. Miami, FL.
University of Central Florida — Department of Computer Science and Cyber Security Division. UCF operates one of the largest collegiate cybersecurity programs in the country, including the nationally dominant Collegiate Cyber Defense Competition team. Orlando, FL.
Florida State University — Department of Computer Science. NSA-designated Center of Academic Excellence; active research in cyber forensics and information security. Tallahassee, FL.
Florida International University — Jack D. Gordon Institute for Public Policy. Policy research on information integrity, disinformation, and hemispheric cybersecurity — directly relevant to the communications dimension of breach response. Miami, FL.
Florida International University — Global Forensic and Justice Center. Research and operational capacity in digital forensics and synthetic media detection. Miami, FL.
Florida Regulatory and Government Resources
Florida Department of Legal Affairs (Office of the Attorney General). The state’s FIPA notification recipient for breaches affecting 500+ Florida residents. myfloridalegal.com
Florida Digital Service (within the Department of Management Services). Florida’s state-level technology and cybersecurity agency; publishes guidance for state agencies that often serves as reference material for the private sector.
Florida Office of Insurance Regulation (OIR). Sector-specific oversight for cybersecurity obligations of insurers operating in Florida.
Florida Department of Financial Services. Relevant for financial-sector breach obligations in Florida-regulated entities.
Professional Associations and Industry Bodies (Florida and National with Florida Chapters)
(ISC)² South Florida Chapter. Professional chapter of the global (ISC)² cybersecurity certification body, serving CISSPs and other certified practitioners in South Florida.
(ISC)² Tampa Bay Chapter. Tampa Bay-area (ISC)² chapter.
(ISC)² Central Florida Chapter. Orlando-area (ISC)² chapter.
ISACA Tampa Bay Chapter. Governance, risk, and information systems audit professionals in the Tampa Bay region. isaca.org/chapters
ISACA South Florida Chapter. Miami / Broward / Palm Beach ISACA professionals.
ISACA Central Florida Chapter. Orlando-area ISACA members.
InfraGard Florida Chapters (Miami, Tampa Bay, Jacksonville, Central Florida). FBI-sponsored public-private partnership for critical infrastructure protection — including cyber threat intelligence sharing. Especially relevant for officers in healthcare, financial services, utilities, and transportation. infragard.org
Florida Bar — Cybersecurity & Privacy Law Committee (Business Law Section). The leading in-state venue for privacy, breach notification, and cyber law practitioners. Highly useful for senior officers selecting outside breach counsel.
Florida Public Relations Association (FPRA). Statewide association running dedicated programming on crisis communication, AI, and online reputation management — including breach-specific workshops. fpra.org
PRSA Sunshine District and Florida Chapters (Miami, Tampa Bay, Orlando, Greater Fort Lauderdale, Palm Beach, North Florida, Gulf Coast). The primary professional network for breach communications practitioners in Florida.
National Resources Particularly Relevant to Florida Officers
CISA (Cybersecurity and Infrastructure Security Agency) — Region 4 (Atlanta), covering Florida. Free incident response support, tabletop exercises, and ransomware guidance. Every Florida senior officer should have their CISA regional contact in their phone. cisa.gov
FBI Cyber Division and Florida Field Offices (Miami, Tampa, Jacksonville). Mandatory point of contact for ransomware, nation-state attacks, and significant intrusions.
U.S. Secret Service Cyber Fraud Task Forces (Florida offices). Particularly active in BEC and financial-fraud investigations.
SANS Institute. Premier cybersecurity training and incident response resources; courses particularly relevant to breach response include FOR508, SEC504, and MGT553. sans.org
Institute for Public Relations (IPR). U.S. research institute publishing work on crisis and breach communications effectiveness. instituteforpr.org
Page Society. Senior-level professional association for Chief Communications Officers; its frameworks are the de facto standard for enterprise-level breach communications governance. page.org
IBM Cost of a Data Breach Report (annual). The most widely cited empirical benchmark for breach cost, response time, and industry impact.
Verizon Data Breach Investigations Report (DBIR, annual). The most widely cited empirical benchmark for breach cause, vector, and pattern.
Selected Works Cited
SEC, “Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure” final rule (Release Nos. 33-11216; 34-97989, July 26, 2023). SEC Division of Corporation Finance, Item 1.05 Compliance and Disclosure Interpretations (December 2023; June 24, 2024). Florida Statutes § 501.171 (Florida Information Protection Act). Verizon, 2025 Data Breach Investigations Report. IBM, Cost of a Data Breach Report 2024. U.S. Congressional Research Service, “The Change Healthcare Cyberattack and Response Considerations for Policymakers” (April 2024). UnitedHealth Group Newsroom, cyberattack updates (March–June 2024). HHS Office for Civil Rights, “Change Healthcare Cybersecurity Incident FAQs.” HIPAA Journal, Change Healthcare coverage (2024–2025). Mandiant / Google Cloud, UNC5537 and Snowflake Customer Instances reporting (2024). Cloud Security Alliance, Top Threats to Cloud Computing Deep Dive 2025. Ragan Communications, “6 Crisis Lessons from Equifax’s Data-Breach Response” (September 2017). Lexology / Newmeyer Dillion, “The Equifax Data Breach: Lessons Learned from a One-Year Look-Back.” Huntress, “Equifax Data Breach: What Happened, Impact, and Lessons.” Fortune, “How companies can learn from Equifax’s 2017 data breach” (August 2023). Bleeping Computer, “MGM Resorts ransomware attack led to $100 million loss, data theft.” CyberArk Labs, “The MGM Resorts Attack: Initial Analysis.” Netwrix, “An Overview of the MGM Cyber Attack.” I-CIO, “Maersk: Springing back from a catastrophic cyber-attack.” CSO Online, “Rebuilding after NotPetya: How Maersk moved forward.” Safety4Sea, “Maersk Line: Surviving from a cyber attack.”
Tags: #DataBreach #CyberSecurity #BreachCommunications #IncidentResponse #FloridaBusiness #SECDisclosure #FIPA #CorporateGovernance #CrisisManagement #ReputationDefense
About Brian French
Led by a commitment to tech-intelligent curation, Brian French tracks and analyzes Business News in Florida that defines Florida's economy. Brian brings an extensive financial background to his analysis, having graduated from the University of South Florida in Finance and serving as a Vice President and Portfolio Manager for Merrill Lynch Private Investors (a division of MLIM) and the Trust Department in St. Petersburg, FL, as well as a Vice President and Trust Investment Officer for SunTrust Bank in Sarasota, FL. His writing blends macroeconomic trends, capital markets analysis, corporate strategy, and modern digital insights for a sophisticated look at Florida's business news and economy.




